Modern security no longer depends on a traditional network perimeter. As organizations adopt cloud services, remote work, and SaaS applications, identity has become the primary security boundary. Microsoft Entra Conditional Access provides a policy-based approach to protect identities and resources while maintaining user productivity.
What Is Microsoft Entra Conditional Access?
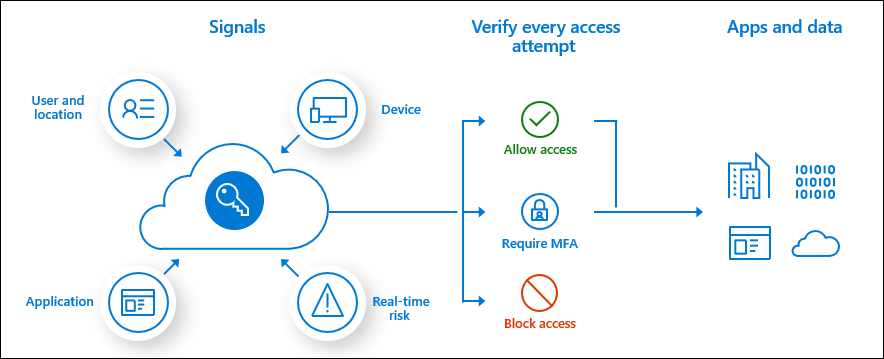
Microsoft Entra Conditional Access is Microsoft’s Zero Trust policy engine. It evaluates multiple signals—such as user identity, device state, location, and risk—before granting access to cloud resources. Conditional Access policies operate as if-then statements.
Conditional Access is enforced after first-factor authentication, using additional signals to determine whether access should be allowed, restricted, or blocked.
Why Conditional Access Is Critical for Zero Trust
Conditional Access plays a central role in Microsoft’s Zero Trust strategy by ensuring that access decisions are not made solely on credentials. Instead, access is dynamically evaluated based on real-time context and risk. This approach helps organizations:
- Reduce identity-based attacks such as credential theft
- Protect sensitive applications and data
- Apply security controls only when needed
- Balance security with user experience
Organizations without Conditional Access are limited to static security controls, while Conditional Access enables adaptive protection aligned with modern threats.
Key Components of a Conditional Access Policy
- Assignments
Assignments define who, what, and under which conditions the policy applies. These include:
. Users and groups – All users, selected groups, directory roles, or guest users
. Cloud apps or actions – Microsoft 365, Azure management, or other enterprise applications
. Conditions – Device platform, location, client app type, sign-in risk, or user risk - Access Controls
Access controls define what must happen before access is granted:
. Grant controls such as multifactor authentication (MFA)
. Device compliance or hybrid join requirements
. Approved client apps or app protection policies
. Block access entirely when conditions are not met
Planning a Conditional Access Deployment
Microsoft recommends a planned and phased approach to avoid unintended access issues. Due to the flexibility of Conditional Access, poor planning can result in lockouts or excessive user friction.
Key planning principles include:
- Clearly defining business and security objectives
- Understanding user personas and access patterns
- Identifying critical applications and privileged roles
- Aligning policies with Zero Trust principles
Microsoft advises against combining Security Defaults and Conditional Access, as both methods serve similar purposes but operate differently. Enabling Conditional Access requires Security Defaults to be disabled.
What Conditional Access Does Security Defaults Provide?
1. Mandatory MFA registration for all users
- All users must register for multifactor authentication.
- MFA registration is enforced across the tenant.
2. Mandatory MFA for administrators
- All privileged roles are required to use MFA.
- This includes access to sensitive administrative services.
3. MFA required when Microsoft detects risk
- Users are prompted for MFA when Microsoft determines it is necessary.
- This is handled automatically by Microsoft risk detection.
4. Blocking legacy authentication protocols
- Legacy authentication (basic auth) is blocked.
- This prevents authentication methods that bypass MFA.
5. Protection of privileged access paths
- Access to privileged operations (such as the Azure / Entra admin portals) is protected.
- MFA is enforced for these high‑risk activities.
Recommended Deployment Phases
Microsoft outlines a phased strategy for deploying Conditional Access safely and effectively.
Phase 1: Foundation and Protection
Start by protecting privileged roles and administrative access. This phase commonly focuses on enforcing MFA for administrators and securing access to core cloud services.
Phase 2: Expand to Users and Applications
Extend protection to regular users and business-critical applications. Policies commonly target sign-in risk, device compliance, and trusted locations.
Phase 3: Optimize and Mature
Continuously review sign-in data, refine policies, and introduce advanced conditions such as risk-based access and session controls. Optimization ensures security remains effective as threats evolve.
Testing and Monitoring Policies
Microsoft strongly recommends using Report-only mode to evaluate the impact of policies before enabling enforcement. This allows administrators to understand how policies would affect users without blocking access.
Ongoing monitoring and testing are essential to ensure:
- Policies continue to meet security objectives
- Business workflows are not disrupted
- New applications and identities remain protected
Conditional Access as an Ongoing Security Practice
Conditional Access is not a one-time configuration. As identity threats evolve, organizations should regularly review and update policies to reflect new risks, applications, and user behavior. Microsoft continuously enhances Conditional Access capabilities to align with modern security guidance.
By adopting a structured planning model and phased deployment, organizations can use Conditional Access to improve security posture while maintaining productivity.
References: https://learn.microsoft.com/en-us/entra/identity/conditional-access/plan-conditional-access


